Cybersecurity Projects
Digital forensic investigations, SIEM threat hunting, and security automation developed during my graduate studies at UNC Charlotte.
SIEM Investigation: SSL Certificate Anomaly Detection
A comprehensive security investigation using the Elastic Stack (Kibana/Elasticsearch) to identify typosquatted Certificate Authorities and potential MITM threats within network traffic logs.

The Challenge
Analyze network traffic logs to identify potentially malicious SSL certificates that could indicate man-in-the-middle attacks or typosquatting attempts.
The Approach
The Impact
Digital Forensics: UNCC Theft Case Examination
A comprehensive forensic examination documenting the recovery of deleted evidence, EXIF metadata analysis, and GPS location tracking using industry-standard tools.
The Scenario
Investigate a simulated theft case involving stolen university property, deleted evidence, digital photos with location data, and timeline reconstruction.
The Investigation
The Results
NetFlow Analysis & Enrichment with Elastic SIEM
A complete security analytics workflow: from raw network log enrichment using Python to advanced threat hunting and visualization in Elastic SIEM (Kibana). Identified suspicious internal hosts involved in potential data exfiltration to unclassified external destinations.
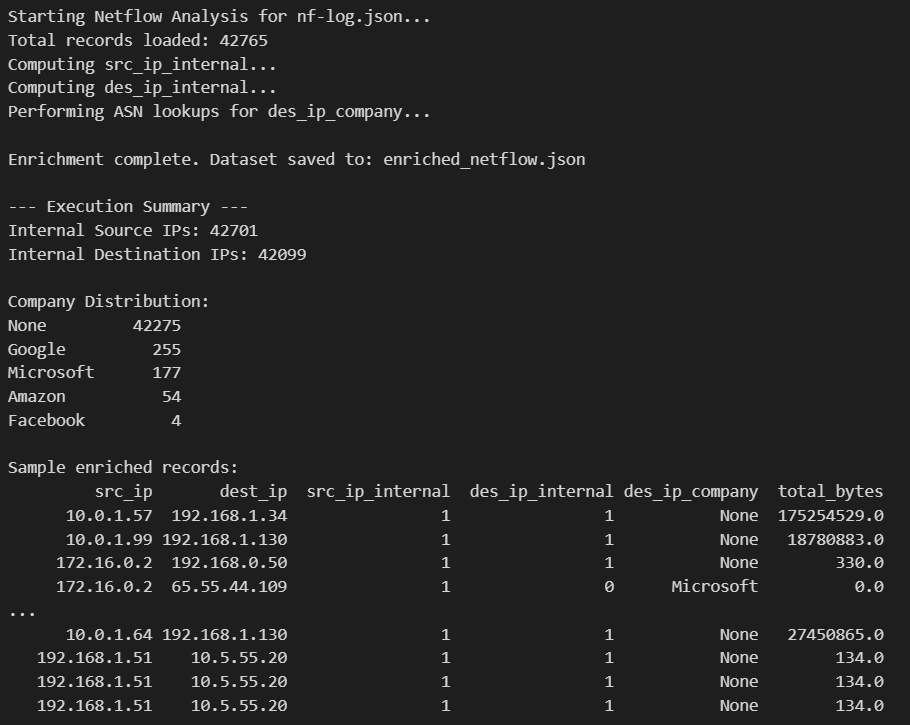
The Challenge
Analyze 42,765 raw netflow records to identify suspicious internal hosts involved in potential data exfiltration or abnormal outbound communication to unclassified external destinations.
The Approach
Key Findings
Visualizations & Evidence
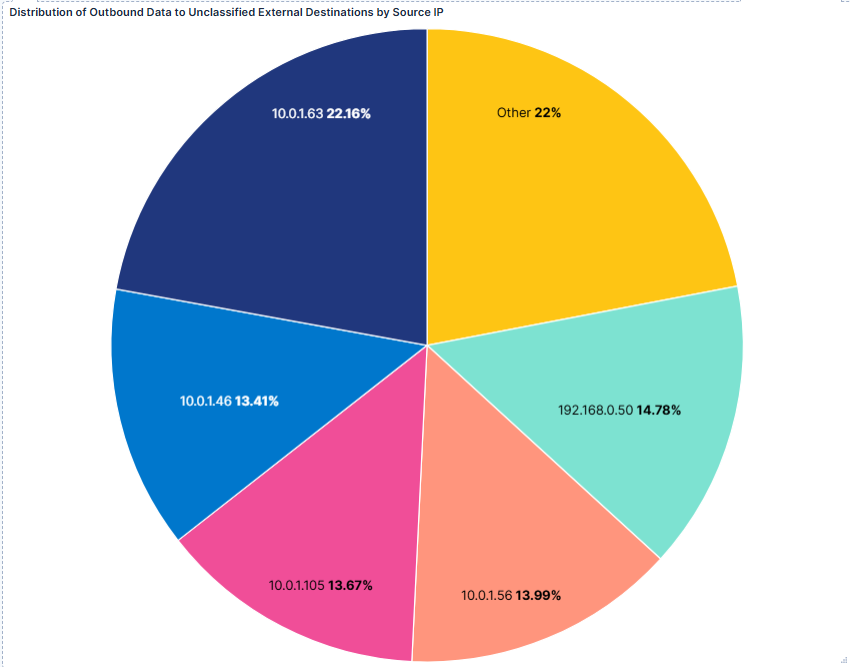
Distribution of Outbound Data to Unclassified External Destinations
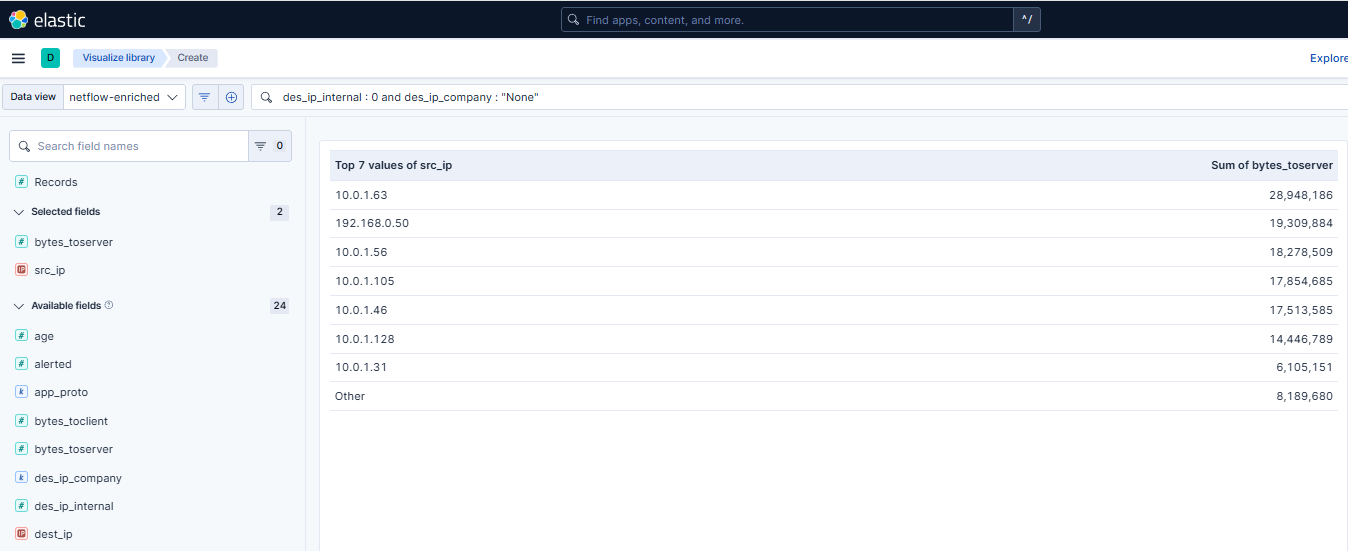
Top 7 Internal Sources by Bytes Sent to External Destinations
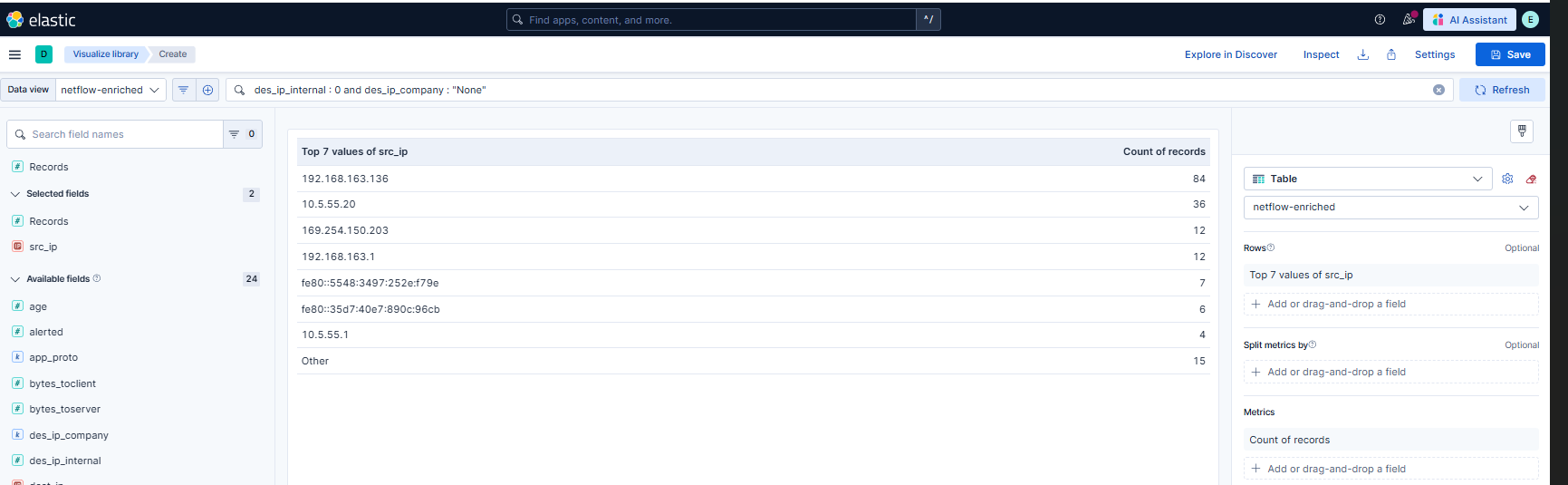
Connection Frequency Analysis — Potential C2 Beaconing Detection
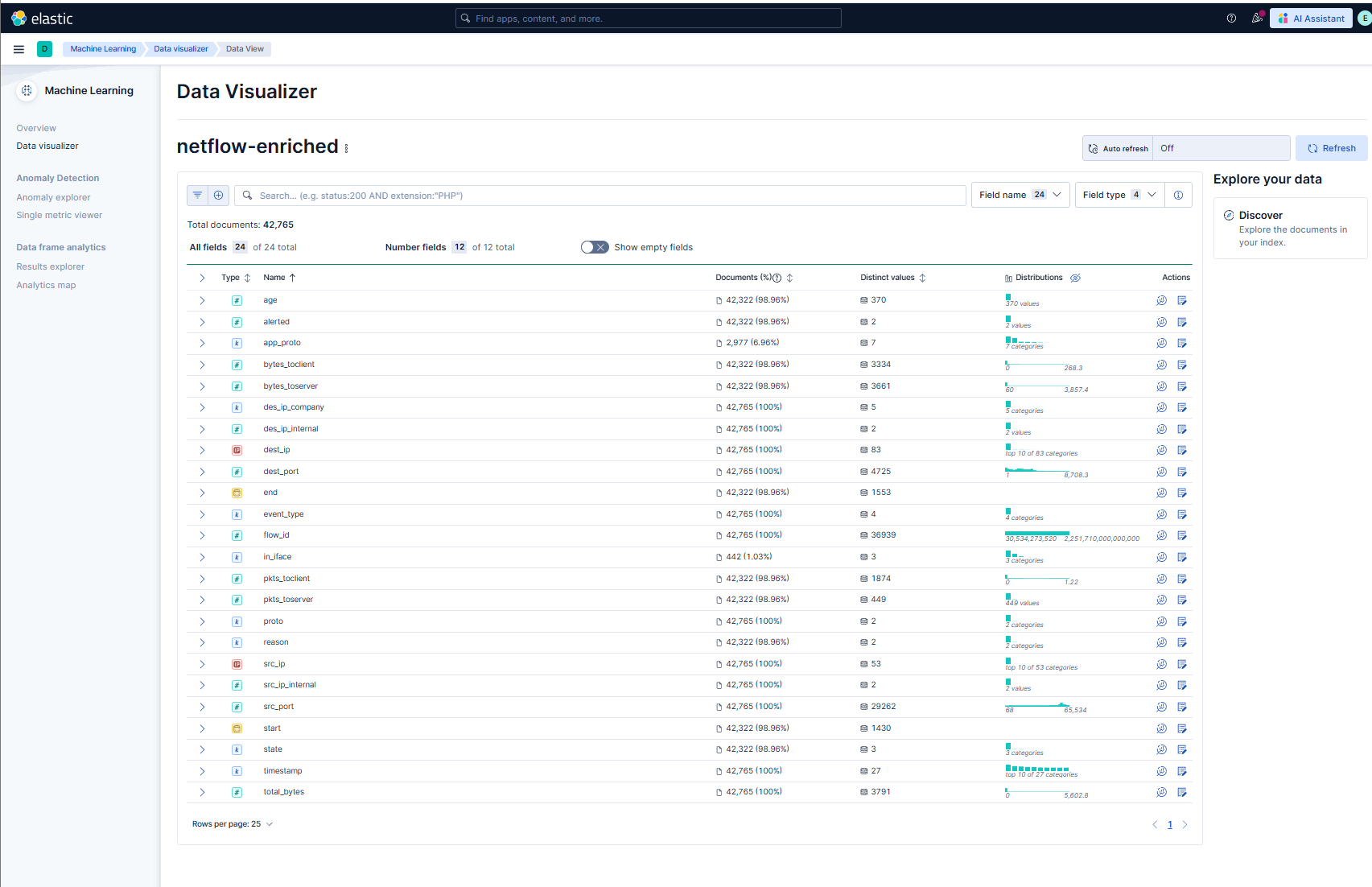
Elastic Data Visualizer — 24 Enriched Fields, 42,765 Documents
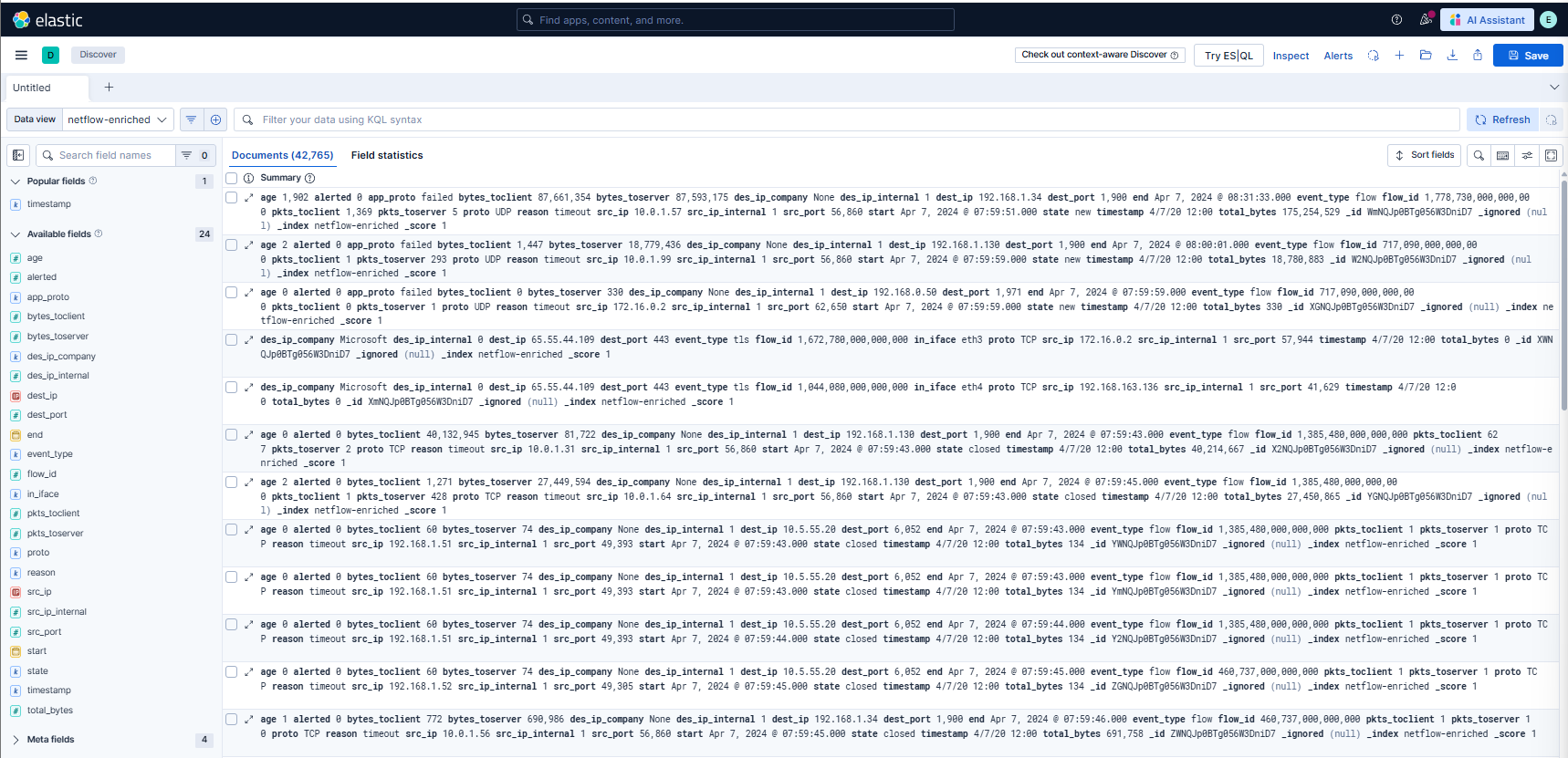
Enriched Netflow Logs in Elastic Discover
Additional Cybersecurity Projects
Log Analysis Automation
Python scripts for automated security log parsing and threat detection.
Vulnerability Assessment Lab
Hands-on penetration testing and vulnerability scanning in controlled lab.
Incident Response Playbook
Documented procedures for common security incidents following NIST framework.
Interested in My Cybersecurity Work?
I'm actively seeking cybersecurity internship opportunities in SOC analysis, digital forensics, or incident response.